All Posts
Hey Alexa, you are a failure
And that’s really sad… Nah, it isn’t.
What if every smartphone had a Peak Carbon app?
And what if it became mandatory?
Here is who spies on your smartphone, thanks to your smart car
Same old, same (depressingly) old. Just with more names.
One password cover to track you all
I can’t believe this stuff exists…
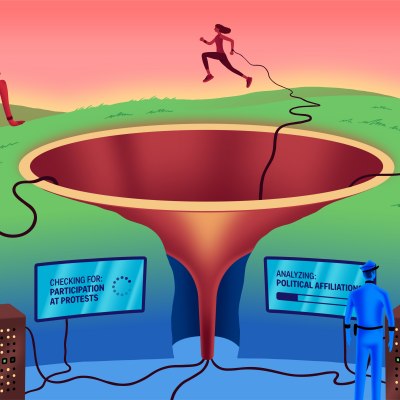
Say no to predictive policing in European law enforcement
Especially when it could become retroactive…
The millionth reason to NEVER buy "your" next car
At least if it’s a new one.